Copy Trading for Beginners: Your On-Chain Starter Guide
New to crypto? Our guide to copy trading for beginners walks you through on-chain strategies, vetting wallets with Wallet Finder.ai, and managing risk.

May 10, 2026
Wallet Finder

March 6, 2026

The fastest way to track profitable wallets and trending tokens.
Anonymous wallets are key players in DeFi, often linked to traders generating returns of up to 340% and profits exceeding $100 million. By analyzing these wallets, you can identify token movements, trading strategies, and market trends before they happen. Tools like Wallet Finder.ai provide real-time alerts, performance metrics, and multi-chain insights to help you make informed decisions.

Wallet Finder.ai is a powerful tool designed to track high-performing blockchain wallets and distill their trading strategies into actionable insights for traders.
Wallet Finder.ai provides a deep dive into wallet performance with metrics like realized PnL, win rates, and risk evaluations. By examining full wallet histories, users can uncover the trading strategies behind successful wallets, including entry and exit points, position sizes, and timing patterns.
The platform also offers real-time tracking with push notifications and Telegram alerts, notifying traders when whale wallets make significant moves. This feature can help users identify opportunities up to 48 hours before the market reacts.
Advanced filtering tools make it simple to pinpoint profitable wallets and trades. These filters work seamlessly with multi-chain data, giving traders a streamlined way to access critical insights.
Wallet Finder.ai supports cross-chain analytics for Ethereum, Solana, and Base ecosystems. Its Discover Tokens feature highlights trending tokens in real time, offering information on token concentration and essential security stats like contract ownership, blacklist status, honeypot risks, and proxy indicators.
This data isn’t just informative - it enhances trading strategies and helps users better manage risk.
Wallet Finder.ai is built to complement data-driven trading and risk management approaches. Users can export filtered blockchain data or complete datasets in formats like CSV or Excel for offline analysis.
The platform also allows traders to mirror the moves of DeFi’s top 1% performers in real time. Custom watchlists can be created to track specific wallets or strategies, enabling users to adapt these insights to their own portfolios. Additionally, traders can connect their own crypto wallets to monitor performance, review historical data, and identify trends for better decision-making.
With a 4.9-star rating from user reviews, Wallet Finder.ai offers a 7-day free trial. While the trial includes limited features and masked wallet addresses, it provides a chance to explore the platform’s potential before committing to a subscription.
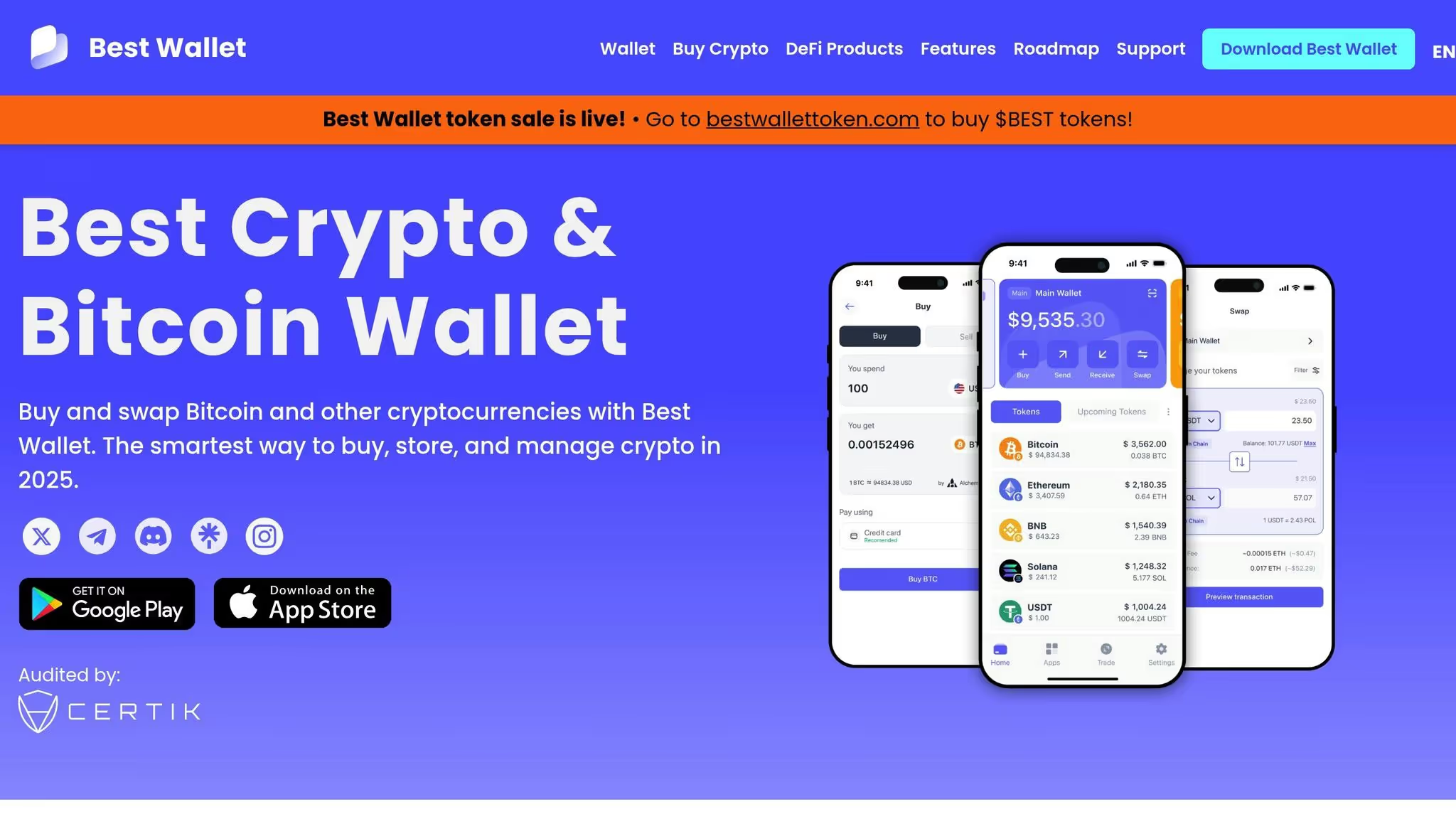
Best Wallet is another option worth considering after WalletFinder.ai, though the available verified information about its capabilities is quite limited.
Details on how Best Wallet analyzes anonymous wallets are scarce. It claims to function as a multi-chain solution, but specifics about its privacy features, supported blockchains, asset tracking capabilities, or integration with trading and risk management tools remain unconfirmed. For the most accurate and updated information, it’s best to refer directly to Best Wallet’s official announcements. This lack of transparency underscores the critical need for reliable, verified data when incorporating wallet insights into algorithmic risk assessments.

Wasabi Wallet stands out by putting privacy above all else, focusing exclusively on secure and anonymous Bitcoin transactions rather than offering a wide range of performance tracking features.
The cornerstone of Wasabi Wallet's privacy approach is its use of the CoinJoin mixing protocol. This technique blends multiple Bitcoin transactions into a single transaction, effectively obscuring the connection between sender and receiver addresses. This makes it much harder to trace individual transaction paths. Additionally, Wasabi routes all network traffic through the Tor network by default, hiding users' IP addresses for an added layer of anonymity. While these features significantly enhance privacy, they come at the cost of reduced transparency for analytical purposes.
Wasabi Wallet is designed exclusively for the Bitcoin network. It does not support Ethereum, other altcoins, or cross-chain transactions. This narrow focus allows it to deliver strong privacy protections for Bitcoin users but limits its appeal for those seeking insights across multiple blockchains. For traders looking to project potential returns on various DeFi protocols, DeFi Yield Estimator provides a practical way to calculate expected gains.
Due to its privacy-first design, Wasabi Wallet is not built for in-depth transaction analysis. The CoinJoin protocol deliberately obscures transaction histories, making it challenging to track wallet performance or discover other wallets. For users who value privacy above all else, this trade-off may be worth it. Up next, we’ll look at a tool that seeks to balance privacy with advanced analytical features.

Using Electrum alongside Tails OS provides a privacy-first approach to analyzing Bitcoin transactions. Tails OS operates entirely from a USB or DVD, ensuring no data is stored on the device, which helps reduce digital traces.
While detailed third-party resources on this setup are scarce, it remains a favored choice among privacy-focused individuals. Tails OS limits data retention, and when paired with Electrum, it adds an extra layer of anonymity. However, users should carefully assess whether this setup meets their specific privacy needs.
Electrum exclusively supports Bitcoin.
Electrum relies on a manual interface, requiring users to review transaction data directly. It does not offer automated analytics or real-time notifications, which often leads users to export data for more in-depth external analysis.
For traders who prefer periodic evaluations, Electrum's data can be exported and integrated into trading and risk models. This method works well for scheduled assessments but is less practical for continuous, real-time monitoring.
CipherTrace is a blockchain analytics tool aimed at helping with compliance and investigative needs. For more detailed information on its features and integrations, refer to its official documentation.
This brief introduction provides context for the comparison table that follows.
When analyzing anonymous wallets, it's essential to consider privacy, blockchain compatibility, analytics features, and integration options. For more insights on improving your analysis workflow, check out our post on Top Tools for Scaling Backtesting which leads the comparison on analytics depth and trading utility. It uses encrypted connections and stores no wallet keys or private crypto data, with only login credentials and survey responses held securely in Amazon AWS Cognito data centers in the United States. It supports Ethereum, Solana, and Base, built on what the platform describes as military-grade infrastructure with expanding network support. Its analytical feature set is the most comprehensive of the five tools: realized PnL tracking, win percentage analysis, risk calculation, wallet performance metrics, token concentration analysis, CSV and Excel exports, Telegram alerts, and API access for custom risk models — all accessible through a single unified interface.
Best Wallet offers built-in privacy controls, encrypted local storage, and optional anonymization features across a multi-chain environment that includes Bitcoin, Ethereum, and Binance Smart Chain. Its analytical capabilities are more limited, covering basic transaction analysis, balance tracking, and portfolio overview, with restricted export options that require manual data extraction. It functions adequately as a self-custody wallet with privacy controls but does not approach the analytical depth of Wallet Finder.ai for active trading use cases.
Wasabi Wallet is built exclusively around Bitcoin privacy rather than analytical capability. Its defining features are CoinJoin mixing, Tor integration, and zero-knowledge proofs, which deliberately obscure transaction histories to protect user anonymity. Its analytical output is correspondingly limited to transaction privacy analysis, mixing effectiveness metrics, and UTXO management, with only manual reporting and no automated integration pathways. Traders seeking Bitcoin transaction anonymization will find it purpose-built for that use case, but its design philosophy makes it unsuitable for the kind of performance tracking and strategy discovery that active DeFi traders require.
Electrum paired with Tails OS provides system-wide anonymization through the Tails operating environment, encrypted wallet files, and proxy support, operating exclusively on the Bitcoin network with access to an extensive range of server options. Its analytical capabilities include advanced transaction analysis, fee optimization, and custom scripting support, but all of these require technical expertise to access through a command-line export workflow. It appeals to technically sophisticated users who prioritize full system anonymization over convenience, but its manual interface and absence of real-time notifications make it impractical for active multi-token trading strategies.
CipherTrace sits in a different category from the other four tools, targeting enterprise compliance and investigative use cases rather than individual trader analytics. It covers over 900 cryptocurrencies and tokens, and its analytical capabilities focus on advanced risk scoring, compliance reporting, and transaction flow analysis, delivered through an enterprise API with custom integration and regulatory reporting tools. For regulated institutions or investigative teams it provides specialized capabilities unavailable elsewhere in this comparison, but its enterprise positioning and compliance orientation make it irrelevant to the copy trading, whale tracking, and DeFi strategy analysis use cases that individual traders are primarily evaluating.
The practical takeaway across all five tools is that analytics depth and trading integration distinguish Wallet Finder.ai from the rest of the field. The privacy-first tools sacrifice analytical transparency by design, the basic wallet offers limited analytical output, and the enterprise compliance tool serves institutional rather than individual trading needs. For traders whose primary objective is identifying profitable anonymous wallets, tracking their strategies, and acting on that intelligence with real-time alerts and multi-chain data, the comparison consistently points toward Wallet Finder.ai as the purpose-built choice for that specific workflow.
Analytics that drive decisions: Wallet Finder.ai stands out with its profitability metrics and real-time insights, offering tools like token concentration analysis and X/Twitter sentiment scoring. These features provide a deeper understanding of market trends, setting it apart from more basic wallet analyzers.
Integration that simplifies workflows: While some platforms rely on manual data extraction, Wallet Finder.ai offers API access, Telegram alerts, and export options, making it easier to incorporate insights into your existing processes.
Blockchain coverage matters: Tools that only support a single chain, like Wasabi Wallet or Electrum, limit the scope of analysis. Wallet Finder.ai’s multi-chain support broadens your perspective, enabling a more comprehensive view of market activity.
Privacy tailored to purpose: Privacy approaches vary widely. Wasabi Wallet focuses on transaction anonymization, while Wallet Finder.ai ensures secure data handling without compromising on analytics depth.
Choosing the right analytics tool can transform how you approach risk modeling and trading strategies, offering the insights and flexibility needed to stay ahead.
The article compares five tools across privacy features, supported blockchains, analytical capabilities, and integration options, establishing a practical selection framework for traders seeking to analyze anonymous wallets. What it does not address is the analytical methodology layer beneath the tool selection decision — the specific techniques that the most sophisticated anonymous wallet analysis applies to extract actionable insights from pseudonymous blockchain data despite the absence of identity information. Advanced anonymous wallet analysis applies three interconnected methodological frameworks that transform raw transaction graphs into structured intelligence about trading behavior, entity identity, and market positioning: graph analytics for relationship mapping, behavioral fingerprinting for strategy identification, and entity resolution for connecting pseudonymous addresses to coherent economic actors.
Graph analytics treats the blockchain as a directed transaction graph where each wallet address is a node and each transaction is a directed edge connecting the sending address to the receiving address, weighted by the value transferred. This graph structure encodes the complete economic relationship history of every address on the network, and applying graph theory algorithms to this structure reveals patterns that are invisible when examining individual transactions in isolation. Degree centrality analysis identifies which wallet addresses appear most frequently as transaction counterparties across the full graph, which reveals addresses that function as hub points in the transaction network — typically exchange deposit addresses, contract addresses, or highly active traders whose positions in the network reflect their role in the broader ecosystem. Anonymous wallets that show high degree centrality in segments of the graph associated with profitable token launches are structurally identified as likely early-information participants even without any identity attribution.
Subgraph clustering identifies groups of wallet addresses that form densely connected transaction communities, meaning they transact frequently among themselves and less frequently with addresses outside the community. These transaction communities often correspond to real-world coordinated groups: developer teams and their associated wallets, investment DAOs and their member addresses, or trading groups whose members share capital and information. A cluster of 15 wallet addresses that transact frequently among themselves but rarely with external addresses, and that collectively enter and exit the same tokens within short time windows, represents a coordinated entity whose aggregate behavior carries more signal weight than any single member address analyzed independently. Identifying these clusters enables the analyst to aggregate the trading activity of all cluster members into a single behavioral profile, revealing the full scope of the entity's market activity and its systematic patterns across many tokens simultaneously.
Behavioral fingerprinting extracts the characteristic trading signature of an anonymous wallet from its observable on-chain transaction patterns, which is the methodology that allows useful analytical conclusions to be drawn about a wallet's strategy and information sources without requiring any knowledge of the wallet's real-world identity. Every trading strategy produces distinctive on-chain behavioral signatures in the timing, sizing, and sequencing of transactions, and these signatures are stable enough over time to serve as reliable identifiers that allow the analyst to recognize when the same strategy is being executed across multiple wallet addresses or to predict what type of transaction is likely to follow a specific observed action.
Entry timing signature analysis characterizes how an anonymous wallet positions its entries relative to token lifecycle events. A wallet that consistently enters new tokens within 0 to 30 minutes of their initial liquidity addition, regardless of the token's narrative, chain, or launch format, is exhibiting a systematic early-entry behavioral fingerprint that strongly implies access to token launch information ahead of public awareness. A wallet that consistently enters tokens after their first social media mention but before their second-day price peak exhibits a momentum-following fingerprint that implies different information sources and strategy logic. Measuring the distribution of entry timing relative to various token lifecycle events across the complete historical trade record produces a timing signature that is characteristic of the wallet's underlying strategy and reproducible enough to allow confident strategy classification.
Position sizing distribution analysis examines the statistical properties of a wallet's position sizes across its complete trade history to identify systematic sizing patterns that reveal risk management methodology and conviction signaling behavior. A wallet that sizes positions using a consistent Kelly fraction of its estimated bankroll, entering larger positions when its win rate history in the current market condition is higher and smaller positions when historical win rates are lower, exhibits a sophisticated risk-calibrated sizing signature that distinguishes it from wallets using fixed position sizes or arbitrary sizing. A wallet that spikes its position size by 3 to 5 times its average on specific trade entries and then returns to average sizing on subsequent entries is exhibiting a conviction spike pattern that identifies its highest-confidence trade entries, which are the specific entries most likely to precede substantial price movements and therefore the most valuable to track for copy trading purposes.
Entity resolution is the analytical process of determining which multiple pseudonymous blockchain addresses are controlled by the same real-world entity, which is essential for forming an accurate picture of any significant market participant because sophisticated traders routinely operate across dozens or hundreds of wallet addresses as a basic operational security practice. An analyst examining only one of a sophisticated trader's 50 operational wallets will see a partial and potentially misleading picture of that trader's total positions, total capital, and behavioral patterns. Entity resolution that correctly identifies all 50 addresses as belonging to the same entity reveals the trader's true scale, complete position book, and full behavioral fingerprint.
Common input ownership heuristic is the most widely applied entity resolution technique for UTXO-based blockchains like Bitcoin, based on the observation that when a transaction consumes inputs from multiple addresses simultaneously, those addresses are almost certainly controlled by the same entity because transaction signing requires the private keys of all consumed input addresses. This heuristic does not apply directly to account-based blockchains like Ethereum and Solana, which require different entity resolution techniques based on transaction relationship analysis rather than input aggregation.
Funding source convergence analysis is the primary entity resolution technique for account-based blockchains, tracing the initial funding transaction of each wallet address being analyzed backward through the transaction history to identify whether multiple addresses received their initial funding from the same source address within a short time window. Two wallet addresses that both received their initial ETH funding from the same source address within the same day are almost certainly controlled by the same entity, because the funder controlled the private key of the source address and deliberately sent funds to both destinations. Extending this analysis through multiple degrees of separation — identifying not just direct funding relationships but funding through intermediate addresses — allows entity resolution to detect more sophisticated address creation patterns where an entity uses multiple hops to obscure the common funding source while still maintaining a traceable transaction path.
Behavioral pattern consistency validation completes the entity resolution process by verifying that addresses identified as belonging to the same entity through funding analysis also exhibit consistent behavioral fingerprints in their trading activity, which provides confirmation that the entity attribution is correct. Two addresses that share a funding source and also show identical position sizing distributions, identical entry timing signatures relative to token lifecycle events, and identical holding period distributions have an exceptionally strong entity attribution confidence because the probability of coincidentally identical behavioral patterns across independent actors is extremely low. Behavioral consistency validation also identifies cases where funding source analysis has produced a false positive entity attribution by revealing that addresses sharing a funding source show distinctly different behavioral fingerprints, which suggests the two addresses are operated by different individuals despite their shared funding origin.
The article's tool comparison identifies the key differentiating features of each platform but does not describe how to integrate multiple tools into a structured intelligence workflow that systematically converts anonymous wallet data into actionable trading signals on a repeatable basis. Anonymous wallet intelligence workflow design addresses the operational questions that determine whether wallet analysis produces consistent edge or inconsistent results that vary with the analyst's energy and attention on any given day: what data to collect, how frequently to collect and process it, what analysis to apply at each cadence, and how to integrate the resulting signals into trading decisions in a way that is systematic rather than discretionary.
The foundational design principle of an effective anonymous wallet intelligence workflow is the separation of data collection, analysis, and decision-making into distinct process stages that operate at different cadences appropriate to their specific requirements. Data collection operates continuously or at high frequency because blockchain data is generated in real time and time-sensitive signals like stealth launch window entries or sudden large position exits require near-real-time detection to be actionable. Pattern analysis operates at lower frequency because the statistical patterns that distinguish high-quality from low-quality anonymous wallets require accumulation of sufficient historical transaction data to produce reliable estimates, and running full behavioral fingerprinting analysis on every new data point would consume disproportionate computational and analyst resources relative to the marginal information gained. Signal integration and trading decision-making operates at a cadence determined by the trader's available execution bandwidth and risk management framework, ensuring that signals are acted upon in priority order without overwhelming the decision-making process with more inputs than can be evaluated at the required quality level.
Continuous monitoring layer is the always-on component of the workflow responsible for detecting time-sensitive events in the anonymous wallets that have been identified as high-priority tracking targets through prior analysis. This layer monitors the Telegram alerts or API event streams from platforms like Wallet Finder.ai for new transaction events in tracked wallets, applying the signal quality scoring framework to each event in real time to classify it into the appropriate response tier. Events meeting Tier 1 criteria are immediately escalated for evaluation against the current market context and the trader's available position capacity, while Tier 2 and Tier 3 events are queued for the periodic analysis review rather than requiring immediate attention.
Weekly behavioral pattern review is the medium-frequency analysis cadence that processes the accumulated transaction data from the prior week across all monitored anonymous wallets to update behavioral fingerprints, identify emerging changes in strategy or timing patterns, and assess whether each wallet's recent activity is consistent with the patterns that justified its inclusion in the high-priority tracking list. A wallet that has been tracked for six months based on its strong early-entry timing signature in new token launches should be reviewed weekly to confirm that its recent transactions continue to exhibit the characteristic sub-30-minute entry timing relative to liquidity addition events, or whether the timing has shifted to later lifecycle stages that might indicate a strategy change or deterioration in its information advantage.
Watchlist tier adjustment is the output of the weekly review process, reorganizing the tracked wallet list based on recent performance evidence to ensure that the highest-monitoring-intensity resources are allocated to wallets currently demonstrating the strongest behavioral indicators of ongoing edge. Wallets that have maintained consistent behavioral fingerprints and strong performance metrics over the trailing 30 to 60 days are retained in the top tier and may have their monitoring intensity increased. Wallets showing strategy drift, declining performance metrics, or behavioral patterns inconsistent with their historical signature are downgraded to lower monitoring tiers, freeing monitoring capacity for newly identified candidate wallets that show promise in initial analysis.
New wallet identification process within the weekly review examines emerging wallet addresses that have appeared in transactions with existing high-priority tracked wallets, which is the most reliable pipeline for discovering new high-performance anonymous wallets before they have built a long enough public track record to be identified through performance-ranking screens. A wallet that has received funding from or made transfers to a known high-performance tracked wallet, and that has subsequently executed transactions exhibiting behavioral fingerprint characteristics consistent with early-information advantage, is a candidate for elevated monitoring status even if its short transaction history does not yet qualify it under the minimum trade count requirements for formal performance ranking. Tracking these second-degree connection wallets with reduced monitoring intensity while their track records develop allows the intelligence workflow to identify emerging high-performance wallets several months before they would appear in public leaderboard rankings.
Signal integration framework governs how the outputs of the continuous monitoring layer and the weekly behavioral review are combined into a prioritized trading signal queue that guides execution decisions without overwhelming the trader with more simultaneous inputs than can be evaluated at the required quality level. The integration framework assigns each signal a composite priority score based on three inputs: the signal quality score from the real-time alert classification, the track record quality score of the anonymous wallet generating the signal, and the market regime compatibility score reflecting whether the current market conditions historically favor the strategy type that the signal-generating wallet employs. Signals scoring in the top decile of the composite priority distribution receive immediate evaluation for execution regardless of total daily signal volume, while signals in lower deciles are processed in sequence during scheduled decision windows.
Position capacity management prevents the signal integration framework from generating more simultaneous position entries than the trader's risk budget and monitoring capacity can support. A trader with a maximum of 10 simultaneous open positions who is currently at 8 positions open has only 2 units of position capacity available, meaning that even if 6 high-quality signals are generated simultaneously, only the top 2 by composite priority score should be evaluated for immediate execution and the remaining 4 should be queued pending capacity restoration from existing position exits. Explicitly managing position capacity as a finite resource that is consumed by entries and restored by exits prevents the common failure mode of overcommitting to too many simultaneous positions during high-signal-density periods when market conditions favor many concurrent opportunities.
Signal decay monitoring tracks how the quality of each open or queued signal degrades over time from the moment of generation, reflecting the empirical observation that the most time-sensitive anonymous wallet signals lose their informational advantage rapidly as the opportunity they identify becomes visible to a wider market participant set. A signal based on a stealth window whale entry in a new token has high quality at the moment of generation and declines sharply over the following 15 to 45 minutes as the token appears on DEX screeners and other tracking tools. A signal based on systematic smart money accumulation over a 3 to 7 day period has lower initial urgency but decays more slowly because the underlying pattern develops over a longer horizon. Applying appropriate signal decay functions to each signal type ensures that queued signals are evaluated for continued relevance before execution rather than being acted upon at the original quality score after the opportunity has partially or fully dissipated.
Delving into anonymous wallets has become a cornerstone of successful DeFi trading and better risk management. The tools we've discussed offer a range of capabilities - from privacy-oriented wallets to in-depth analytics platforms - designed to extract meaningful insights from blockchain data.
By leveraging the analytics described earlier, traders can fine-tune their strategies. These tools combine real-time data with historical trends, enabling users to analyze key factors such as entry and exit points, position sizes, and the trading patterns of high-performing wallets. This approach offers actionable insights drawn directly from some of the best players in the DeFi space.
Relying on this data-driven perspective not only improves trading strategies but also enhances risk evaluation. Instead of depending solely on market sentiment, traders can make decisions based on tangible metrics like profit and loss figures, win rates, and risk assessments from proven performers. This reduces the uncertainty that often comes with DeFi trading.
Platforms like Wallet Finder.ai take it a step further by integrating multi-chain analytics, real-time alerts, and customizable data exports. These features ensure your strategy remains flexible and thorough. Whether you're designing personalized risk models or replicating successful trades, access to filtered blockchain data across Ethereum, Solana, and Base opens up new opportunities while reducing blind spots.
WalletFinder.ai empowers traders with real-time alerts that highlight major market shifts, ensuring users can act swiftly when opportunities arise. The platform also delivers in-depth performance metrics and access to historical data, allowing traders to make well-informed decisions and fine-tune their strategies with precision.
By monitoring wallet performance and examining trading behaviors, WalletFinder.ai helps users maintain a competitive edge in the ever-changing landscape of DeFi trading.
WalletFinder.ai places a strong emphasis on user privacy, employing encrypted connections to keep all data secure throughout the analysis process. Importantly, the platform does not retain wallet keys or any sensitive cryptocurrency data, allowing users to explore anonymous wallets with confidence.
The only data stored includes necessary details like login credentials and survey responses, which are securely managed in Amazon AWS Cognito data centers based in the United States. This setup adheres to stringent security protocols, ensuring user information remains protected and confidential.
Multi-chain support plays a crucial role in analyzing anonymous wallets, offering a comprehensive view of wallet activity across different blockchain networks. Each blockchain often features distinct assets, transaction types, and trading behaviors, all of which can significantly influence your analysis.
WalletFinder.ai simplifies this process by combining data from leading DeFi blockchains like Ethereum (ETH), Solana (SOL), and Base into a single, user-friendly platform. This integration enables users to effortlessly evaluate wallet performance and trading patterns across various networks, uncovering key insights and empowering smarter decision-making.
Three interconnected methodologies transform pseudonymous blockchain data into structured wallet intelligence without requiring identity attribution. Graph analytics treats the blockchain as a directed transaction network where addresses are nodes and transactions are weighted edges, applying degree centrality analysis to identify hub-point addresses and subgraph clustering to identify transaction communities that correspond to real-world coordinated groups. A cluster of wallet addresses that transact frequently among themselves and collectively enter the same tokens within short windows represents a coordinated entity whose aggregate behavior is far more informative than any individual address analyzed in isolation, because it reveals the full scope of the entity's market activity and its systematic patterns across many tokens simultaneously.
Behavioral fingerprinting characterizes an anonymous wallet's trading strategy through three signature types derived from its complete transaction history. Entry timing signature measures the distribution of the wallet's trade entry times relative to token lifecycle events, distinguishing consistently sub-30-minute stealth window entrants with likely early-information advantage from momentum followers entering after social media visibility. Position sizing distribution analysis identifies whether the wallet uses risk-calibrated sizing with conviction spikes on high-confidence entries or fixed sizing without strategic variation, with conviction spike entries being the most valuable for copy trading identification. Entity resolution completes the methodology by connecting multiple pseudonymous addresses to the same real-world economic actor using funding source convergence analysis, tracing initial funding transactions backward to identify addresses sharing common funding origins, and validating entity attributions through behavioral pattern consistency verification that confirms independently identified addresses show matching fingerprint characteristics.
An effective anonymous wallet intelligence workflow separates data collection, pattern analysis, and signal integration into distinct process stages operating at cadences appropriate to their specific requirements. The continuous monitoring layer operates in real time through platform APIs or Telegram alert feeds, applying signal quality scoring to every new transaction event from tracked wallets to classify each into immediate evaluation, queued review, or watchlist-only tiers based on its composite quality score. The weekly behavioral pattern review processes accumulated transaction data to update behavioral fingerprints for all monitored wallets, identify strategy drift or performance deterioration that warrants watchlist tier adjustment, and screen second-degree connection wallets from transactions with existing high-priority targets as a new wallet discovery pipeline.
Signal integration combines real-time monitoring outputs with weekly review insights into a prioritized execution queue using a composite priority score that weights the individual alert's quality score, the generating wallet's track record score, and the current market regime's compatibility with the wallet's historically demonstrated strategy type. Position capacity management prevents overcommitment during high-signal-density periods by treating available position slots as a finite resource that limits simultaneous execution candidates to what the trader's risk budget and monitoring capacity can support. Signal decay monitoring tracks how quickly each signal type loses its informational advantage after generation — stealth window signals decay within 15 to 45 minutes as token visibility spreads, while multi-day accumulation signals decay over hours — ensuring queued signals are re-evaluated for continued relevance before execution rather than acted upon at their original quality score after the opportunity has partially dissipated.